Can I ship this AI change?
The first screen should answer the release question in plain language, then name the next useful proof. Raw JSON stays available for automation and audit, but it is not the primary user experience.
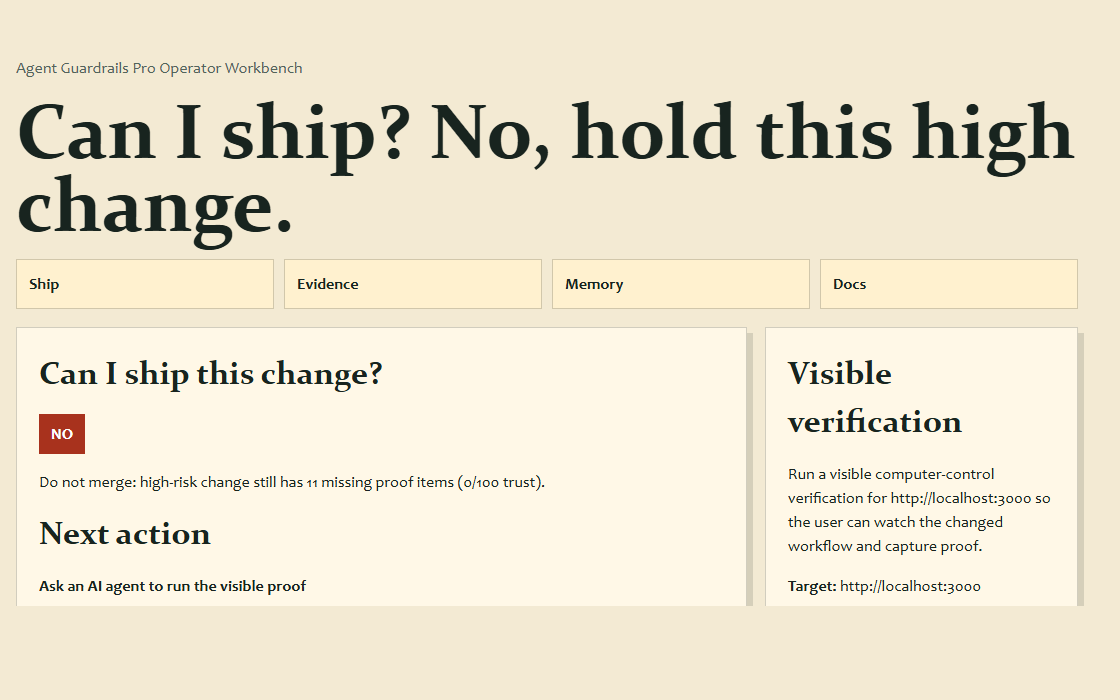
Agent Guardrails Pro turns AI-generated code changes into a go-live verdict: what can ship, what proof is missing, and the cheapest evidence that can unblock the release.
check --json
pro status
pro report
pro workbench --open
The first screen should answer the release question in plain language, then name the next useful proof. Raw JSON stays available for automation and audit, but it is not the primary user experience.
The user is not feeding evidence to satisfy the tool. Pro turns the existing release question into a short briefing: what changed, what risk is real, and what proof is worth running next.
The user runs `agent-guardrails check` from the repo. If Pro is active, the output starts with the go-live answer instead of making the user inspect JSON.
Pro names the cheapest useful proof and generates an agent prompt, so Codex, Claude Code, OpenCode, or another agent can run or watch the proof instead of the user typing every command.
The report records why the decision changed, where evidence was saved, and what remains risky, so the user has a release note and future repo memory without writing a separate checklist.
OSS catches scope and safety issues. Pro explains whether the change can go live, why that verdict is trustworthy, and how to close the gap with the least work.
Verdict-first output: go, need evidence, or hold. Users should not read a pile of checks to infer whether deployment is safe.
Ordered evidence steps grouped by API, UI, data, auth, async, deploy, scope, and validation surfaces.
Pro remembers which evidence closed prior gaps, then recommends proven local commands when similar risk appears again.
Agent Guardrails Pro is designed for solo builders and small teams that use Codex, Claude Code, Cursor, OpenCode, or other AI coding tools.
Use the OSS command you already trust. Pro enriches it when installed and licensed.
Follow the cheapest next proof instead of guessing which test, browser check, or rollback note matters.
Show a buyer-readable go-live report that captures accepted evidence, missing risk, and the decision trail.
$ agent-guardrails check --review
Go-live verdict: HOLD (high)
Cheapest proof: npm test -- auth
Trust receipt: missing allow/deny permission evidencePro is not trying to replace your coding agent. The Workbench is the sidecar that keeps ship state, evidence, repo memory, and public docs aligned.
Can I ship, why not, and the one action that can change the verdict.
Commands, screenshots, rollback notes, and visible verification records that already matter for release confidence.
Public documentation update plans stay separate from local-only notes, issue logs, and generated sandbox artifacts.
For UI, browser, terminal, and desktop-visible changes, Pro can recommend a visible computer-control verification plan so the user can watch an AI agent perform the critical path.
Pro names the target surface, visible command or harness, watch points, and screenshot or video evidence paths.
Hand the generated prompt to Codex, Claude Code, OpenCode, or another computer-control-capable agent.